Open Source Summit 2022
Takeaways & Learnings
June 23, 2022

We just attended the Open Source Summit in June 2022, hosting in Austin TX. First I wanted to start of by thanking the Linux Foundation for having this conference. The LF events in particular are my favorites. The content surrounding the Open Source Summit strikes particularly close to our hearts. I’m thrilled to see so much activity around improving the security of the open source ecosystem. Based on the talks we attended, here are some of my key takeaways from this event.
Supply Chain Security is Becoming a Buzz-word
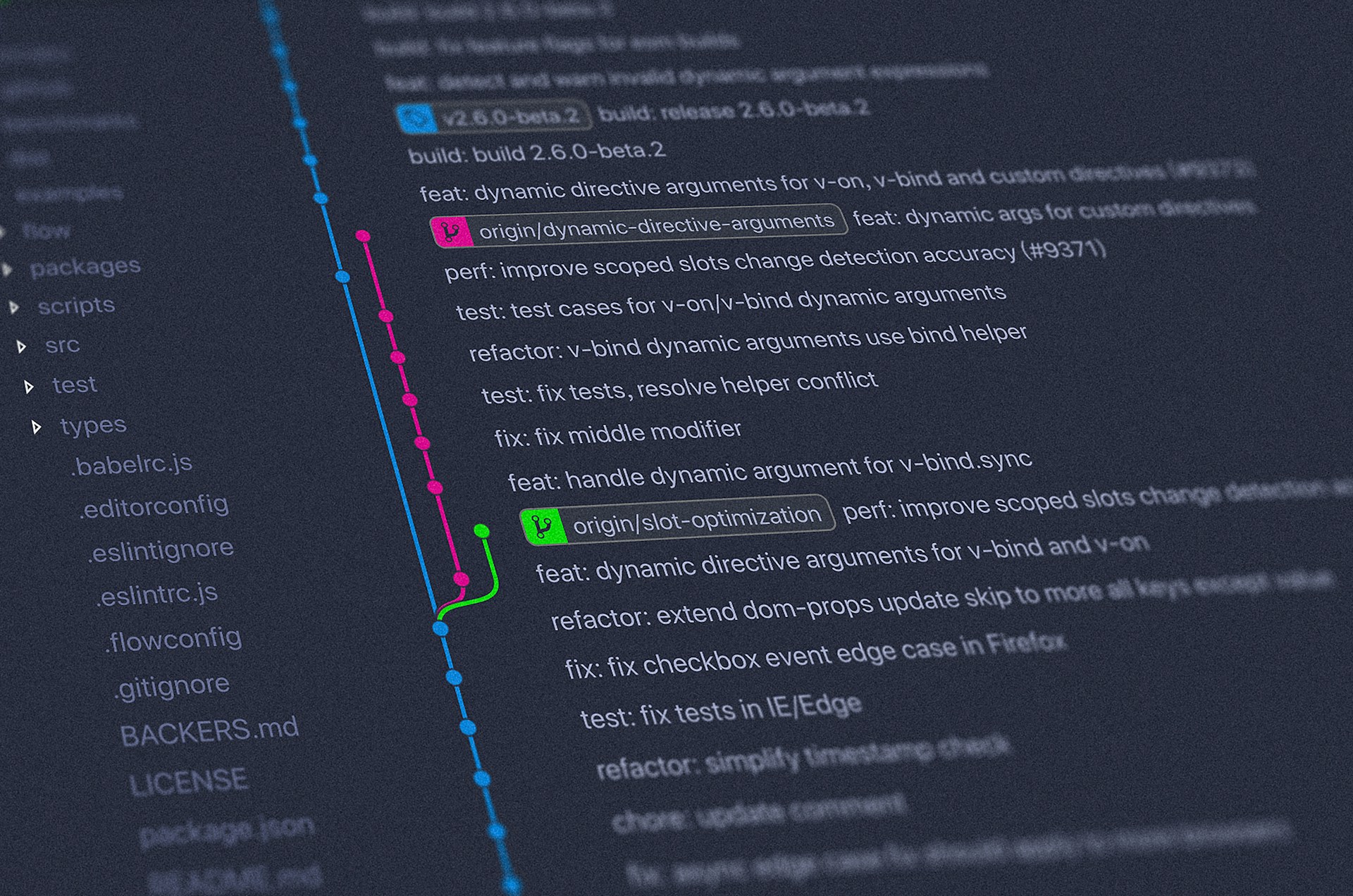
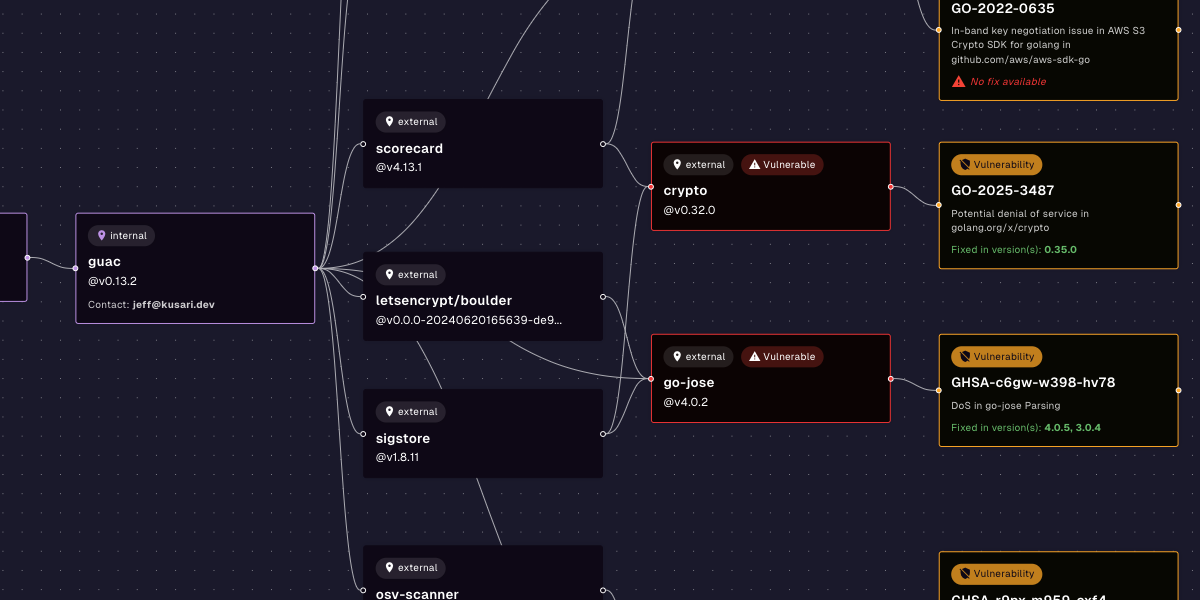
It was hard to walk around the vendor floor and NOT find companies pushing Supply Chain Security in one way or another. I personally find it interesting how many different interpretations folks have on what this means. I see this as a bit of a double-edged-sword. On one hand, it’s helping the topic get out there, and it is critically important that this happens. On the other hand, if there were 20 different vendors selling Supply Chain Security, there were 20 different explanations of what the problem is. We need to be coming together a bit more to really drive home what Supply Chain Security actually means. In my humble opion, it’s more than just scanning for CVE’s on artifacts you already have in your repository. I’d love to work with others in the field to push for more clarity and agreement around this. If we want to collectively solve this problem we first have to agree on what the problem actually is first, and I think we have some work to do there.
Companies are Wrestling with how to Secure their Supply Chain
If you are returning to work on Monday and confused on how to take action on all the things you learned here, you’re definitely not alone. From organizing internal teams and getting difficult processes changed to the inner workings of SPIRE and what even is an SVID anyway, the confusion is real. This is a massively complicated area, and feeling lost should not make you feel bad. You should be proud of yourself for being on the leading edge of a problem that has both too few and too many answers for every question you come across.
The issues and threats arounds supply chain security are many and can be complex to comprehend. It cannot be solved by adding another vulnerability scanner but need a more comprehensive approach. In the near future we hope to bring forth solutions that provide this comprehensive solution without being overly complicated to implement. Supply chain security (as with any security implementation) should not be a burden on the organization or the developers, but rather a seamless piece in an ever evolving ecosystem.
Curation and Establishing Trust
One of the more interesting technical keynotes I enjoyed was from Eric Brewer, Vice President of Infrastructure at Google. The tl;dw is that Google is going to be building a curated open source repository where they will be monitoring vulnerabilities in common libraries, and more importantly patching them as they need. The focus on a curated Open Source repository is a very exciting prospect for all of us. Additionally I think it should make everyone ask - why do you trust what you trust? Are you confident that the team managing the libraries you use are doing a good job? Do you trust how they are taking in their dependencies? Have you looked at the processes that they follow, or do you trust their reputation? I’m excited to see someone with the scale and engineering horsepower of Google to take on such a big piece of the infrastructure for Open Source Software. But as a second order consequence, I’m hoping more folks look at their own dependency sources with far more scrutiny.
Shameless Plug for Parth & Brandon
If you weren’t able to attend in person - I would highly recommend watching the Road to SLSA3: Non-falsifiable Provenance in Tekton with SPIFFE/SPIRE. This was given by our own Parth Patel, as well as Brandon Lum from Google. It was a great practical demonstration of some of the work they’re pushing into the open source community to facilitate the level of assurance SLSA 3 can bring.
I will update this blog with the youtube link once it is made available.
Personal Connections are Invaluable
As much as I love remote work - while I was in Austin I met many folks who I had worked for over a year for the first time. To all who took the time to connect with me while I was out there, thank you. Even if it was brief it meant the world to me to see all of you in person again.
Previous
No older posts
Next
No newer posts

















.webp)









.webp)























.png)
.png)




.png)
.png)
.png)
.png)
.png)
.png)
.png)



.png)









.jpg)